Biometrics, an overview
At Humanode, we’re using biometrics to enable sybil resistance. This technology will ensure fair distribution of power and governance in distributed systems like blockchains.

Based on The International Organization for Standardization (ISO), biometrics is defined as the automated recognition of individuals based on their biological and behavioural characteristics.
Individuals are labeled and described using biometric identifiers, which are unique, measurable features. Physiological characteristics, which are related to the shape of the body, are typically used to classify biometric identifiers. Fingerprints, palm veins, facial recognition, DNA, palm print, hand geometry, iris identification, retina, and odor/scent are just a few examples. Typing rhythm, gait, keystroke, signature, behavioral profiling, and voice are all examples of behavioral characteristics that are related to a person's pattern of behavior. The term 'behaviometrics' was created by some researchers to denote the latter type of biometrics.
Token-based identity systems, such as a driver's license or passport, and knowledge-based identification systems, such as a password or personal identification number, are more traditional methods of access control. Biometric identifiers are more reliable in validating identity than token and knowledge-based approaches since they are unique to each individual; yet, the gathering of biometric identifiers raises privacy concerns concerning the final use of this information.
Biometric authentication (also known as realistic authentication) is a type of identification and access control used in computer science. It's also utilized to track down individuals in groups that are being watched.
Types of Biometrics:
- DNA: An individual's identity is determined by analyzing DNA segments.
- Eyes (Iris, Retina): The use of characteristics discovered in the iris to identify a person. Vein patterns in the back of the eye can also be used.
- Face: The study of face traits or patterns in order to verify or recognize a person's identity. Either eigenfaces or local feature analysis are used by most face recognition algorithms.
- Fingers (Fingerprint, Geometry): The ridges and valleys (minutiae) on the surface tips of a human finger are used to identify a person. The use of 3D geometry of the finger can also be used to determine identity.
- Gait: The use of a person's stride or walking pattern to determine their identity.
- Signature: The analysis of handwriting style, particularly the signature, to verify an individual's identity. Static and Dynamic digital handwritten signature authentication are the two main forms. A visual comparison of one scanned signature to another scanned signature, or a scanned signature versus an ink signature, is known as static. Two scanned signatures can be checked using advanced algorithms using technology.
- Typing: The use of a person's unique typing traits to establish identity.
- Vein: Vein recognition is a sort of biometrics that uses the vein patterns in the human finger or palm to identify individuals.
- Voice - Speaker: The use of speech as a means of determining a speaker's identification for access control. If the speaker claims to be someone else and the voice is utilized to corroborate that claim. A 1:1 match occurs when one speaker's voice is matched to a single template (also known as a "voice print" or "voice model"). Speaker verification is frequently used as a "gatekeeper" to allow access to a secure system (e.g.: telephone banking). These systems work with the user's knowledge and usually necessitate their participation. When a person presents their passport at border control, for example, the agent checks the person's face to the photograph on the document.
This is how Humanode classify the modalities:
Identification Metrics
Adapted from Humanode Whitepaper
Biometrics examples in use
Aside from the fact that biometrics are employed in many smartphones nowadays, biometrics are used in a variety of fields. Biometrics are employed in the following sectors and organizations, for example:
- Law Enforcers. It's utilized in criminal identification systems like fingerprint or palm print authentication.
- Airport Security. Biometrics, such as iris recognition, are sometimes used in this industry.
- Healthcare. It is utilized in systems that require fingerprints for identification, such as national identity cards and health insurance schemes.
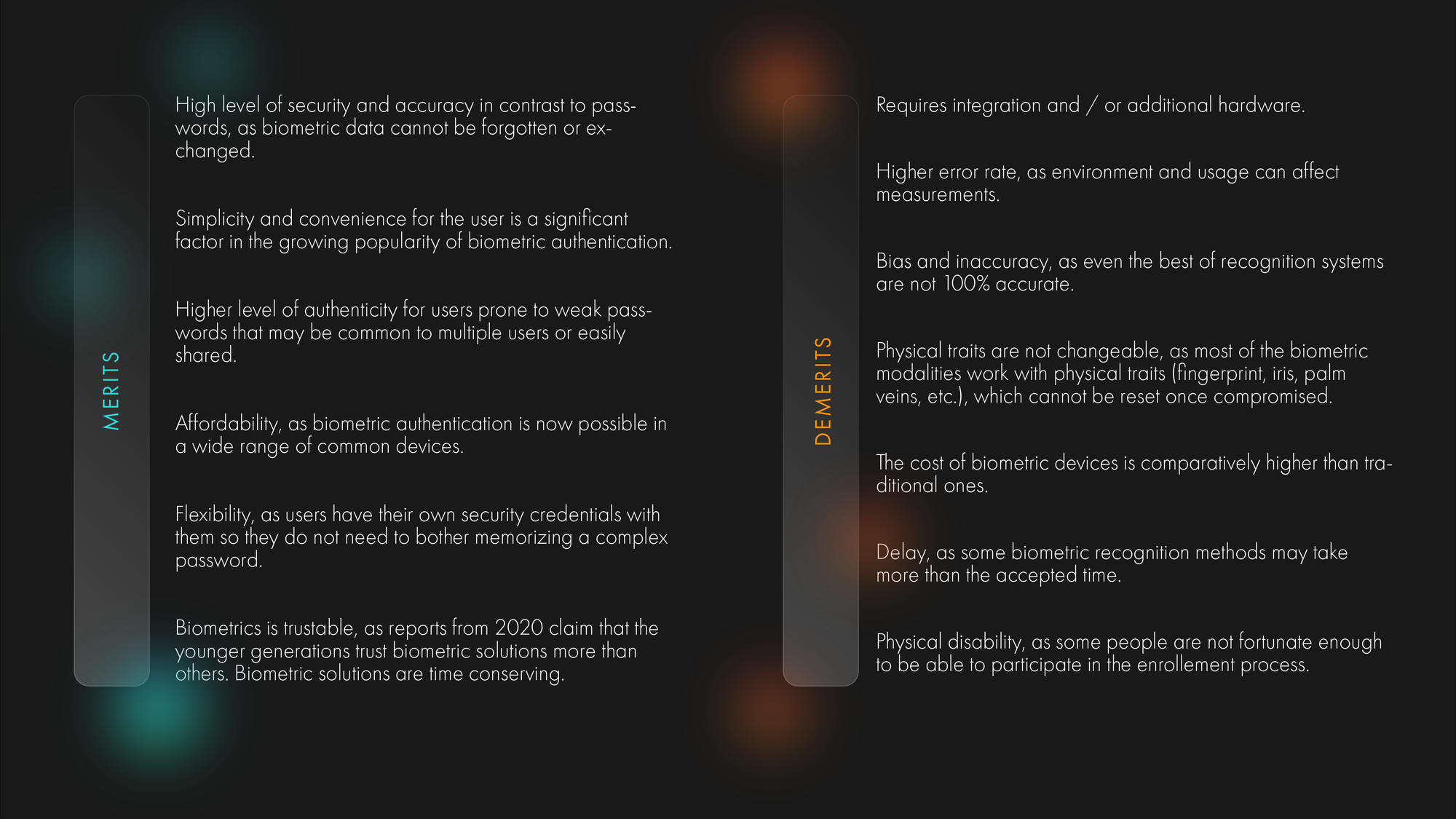
Biometrics' pros and cons
Biometrics, which is the discipline of analyzing physical or behavioral features unique to each people in order to recognize their identity, provides numerous advantages. However, biometric authentication comes with various hazards, which are listed below.
Private biometrics
Biometric identification systems posed a significant threat to personal privacy until recently. Biometric data is regarded highly sensitive since it may be linked to a single person. Passwords aren't considered PII (Personally Identifiable Information) because they can be changed and aren't linked to any specific individual. In the past, the main risk of biometric matching was that it required the biometric data to be displayed at some time during the procedure.
Even at the lowest level of contact, a malicious actor is unable to circumvent a private biometric system since the plaintext communication line is separated from all others. Biometric data is ephemeral at inception in this situation, which means that biometrics exist for a fraction of a second or a few seconds, depending on the device, and are never saved.
Privacy and security considerations
Face recognition is now the main method which has the highest accuracy and the most developed liveness detection, that is why we focus on facial recognition, with plans of adding other methods later on.
Acceptance of the biometric element may also be influenced by its stability. Fingerprints do not change over time, although the look of the face can alter dramatically due to age, disease, or other circumstances. The most serious privacy concern with biometrics is that physical characteristics such as fingerprints and retinal blood vessel patterns are usually static and cannot be changed. Nonbiometric elements, such as passwords (something a person knows) and tokens (something a person has), on the other hand, can be replaced if they are breached or otherwise compromised. The 2014 data breach at the US Office of Personnel Management (OPM) exposed the fingerprints of nearly 20 million people, demonstrating the challenge.
While biometric scanners are improving in terms of quality, they can still create false negatives when an authorized user is not identified or authenticated, as well as false positives when an unauthorized person is recognized and authenticated.
At Humanode, we’re using biometrics to enable sybil resistance. This technology will ensure fair distribution of power and governance in distributed systems like blockchains.
References: