Comparative Analysis of Different Proof of Personhood (PoP) Protocols

The current landscape of decentralized networks isn’t without its flaws. A notable issue is the emergence of a plutocracy within certain consensus mechanisms. In systems like Proof of Stake or Delegated Proof of Stake, the power often concentrates in the hands of a few – those who hold substantial crypto assets.
This concentration of power contradicts the very ethos of decentralization, turning these networks into echo chambers of the wealthy, and raises questions about the equity and fairness of these systems. Then, there are issues like Sybil attacks, where someone uses multiple accounts or bots to game the system.
A feasible solution presented to resolve these issues is the establishment of digital identities. And in this article, we’ll be analyzing different protocols working on establishing digital identities in the decentralized world. So let’s delve into it.
In this intricate dance of digital identity within the world of decentralized protocols, the echoes of Fyodor Dostoevsky's profound question in 'The Brothers Karamazov' – 'Who am I?' – resonate more than ever. In this classic novel, the characters wrestle with existential questions that now find a parallel in our struggles with identity in the digital age.
The quest to establish 'who we are' online has become a critical challenge, pivotal to the integrity and functionality of the web, in particular the decentralized web. How you may ask?
As Edward Snowden pinpointed the core vulnerability in modern systems: 'The one vulnerability being exploited across all systems is identity.' This insight is particularly relevant in the context of blockchain and decentralized networks, where the assurance of identity is not just a privacy concern but a cornerstone for securing trust and legitimacy in every transaction and interaction.
In recent years, many solutions to deal with the challenge of establishing digital identity or Proof of Personhood have emerged, promising to solve the underlying issues in the present blockchain protocols while preserving anonymity – an essence of decentralization.
Our exploration, 'Comparative Analysis of Different Proof of Personhood (PoP) Protocols,' delves into the most prominent PoP protocols. The aim is to provide a comprehensive analysis of how various PoP protocols operate and how they differ. Join us in this journey.
What is Proof of Personhood (PoP)?
At its core, PoP answers a fundamental question in the digital world: How do we know you are uniquely you? While in traditional systems, identity is often proven through documents or biometrics, but in the decentralized realm of Web3, where trust is not anchored in centralized institutions, proving individuality becomes a complex puzzle. But do you know PoP protocols are designed to solve this puzzle? How, you may ask? Let me lay it down for you.
They ensure that each participant in a network is a unique human being, without necessarily revealing their real-world identity. This concept is not entirely new; it has its roots in early discussions about digital identity and privacy. However, it has gained significant traction with the rise of blockchain technology and decentralized systems, where the need for trustless, equitable participation is paramount.
The evolution of PoP is a response to the limitations of traditional digital identity verification methods, which often rely on personal data collection, leading to privacy concerns, or on economic resources, creating barriers to entry. PoP protocols, on the other hand, aim to create a more inclusive and equitable digital space by focusing on the uniqueness of individuals rather than their data or wealth. But why are they considered so important in the decentralized web? Let's learn.
Importance in Web3
In the decentralized architecture of Web3, PoP becomes crucial for several reasons:
- Preventing Sybil Attacks: In decentralized networks, one common threat is the Sybil attack, where a single user creates multiple accounts or nodes to gain disproportionate influence. PoP protocols safeguard against this by ensuring that each participant has equal representation, regardless of their technical or financial capabilities.
- Enhancing Governance: Web3 is not just a technological revolution; it's a shift towards more democratic and decentralized governance models. PoP contributes to this by ensuring that governance decisions, voting, and resource allocation are based on the principle of one person, one vote, thereby promoting fairness and avoiding plutocracy.
- Equitable Resource Distribution: In Web3, resources like bandwidth, computational power, or even digital currency are often distributed among network participants. PoP ensures that this distribution is done equitably, allowing equal access and opportunity to all users, not just those with the most resources or technical know-how.
- Building Trust and Community: By verifying the unique human presence behind each digital interaction, PoP fosters a sense of trust and community. In a decentralized world, where central authorities do not govern interactions, this trust is essential for collaboration, commerce, and social interaction.
In summary, PoP is more than just a technical solution; it's a philosophical cornerstone of the Web3 ecosystem. It strives to create a digital environment where each individual's presence is recognized, valued, and protected, paving the way for a more democratic, equitable, and trust-based online world. As we delve deeper into the different protocols in the next sections, we will explore how this vision is being turned into a tangible reality.
Comparative Analysis of Proof of Personhood (PoP) Protocols
In the burgeoning world of Web3, several PoP protocols have emerged, each with its unique approach to validating individuality. Among the noteworthy are Anima, BrightID, Idena, Proof of Humanity, WorldCoin, and Humanode. These protocols represent a cross-section of strategies employed to tackle the challenge of digital identity in decentralized environments.
Comparison Criteria
To evaluate these protocols, we'll focus on six key criteria:
i. Security: How effectively does the protocol protect against fraud and misuse?
ii. Accuracy: How effectively does each protocol correctly identify unique individuals?
iii. Privacy: Does the protocol safeguard users' personal information and anonymity?
iv. Scalability: Can the protocol accommodate a growing number of users without compromising performance?
v. Accessibility: How easy is it for individuals from various backgrounds to use the protocol?
vi. User Experience: Is the protocol user-friendly, and what is the overall experience for the end-user?
Protocol Breakdown
- Anima
- Security: Ensures strong security against identity fraud by using Synaps-issued VCs linked to crypto wallets with blockchain encryption and wallet signatures.
- Accuracy: Achieves high verification accuracy through biometric data, official ID documents, and its unique FaceGraph technology.
- Privacy: Prioritizes privacy by securely storing identity attributes in decentralized systems called Storj, minimizing personal information exposure.
- Scalability: Utilizes lightweight verification process and multichain compatibility, including BNB and Cosmos, to enable effective scalability across various blockchain networks.
- Accessibility: Highly accessible, integrating with various wallets like MetaMask, Ledger, Coinbase, Coin98, and MultiversX for simplified user interaction.
- User Experience: Offers a streamlined user experience, enhanced by a recent update allowing public/private key generation directly from wallet signatures.
- BrightID
- Security: Utilizes social graph theory to establish unique identities, reducing the risk of Sybil attacks.
- Accuracy: Relies on a social graph to verify individuality. However, its accuracy can be influenced by the user's network size and connectivity, potentially leading to false positives or negatives in sparse or highly interconnected networks.
- Privacy: Prioritizes user privacy by not requiring personal information for verification.
- Scalability: Designed to scale with an increasing user base, though its reliance on social connections may limit rapid expansion.
- Accessibility: Requires users to build a network of connections, which can be challenging for newcomers.
- User Experience: Provides a straightforward app-based interface, but building a sufficient network can be time-consuming.
- Idena
- Security: Employs a novel “Proof of Identity” mechanism through regular, short, synchronized tests (flips).
- Accuracy: The unique approach of flip tests ensures a high degree of accuracy in verifying human presence. However, the accuracy might vary based on the users' interpretation and understanding of the flips, which can be subjective.
- Privacy: Users remain anonymous, but participation in the network requires active and timely engagement.
- Scalability: Scalability is a challenge due to the synchronous nature of the flips.
- Accessibility: Requires consistent and timely participation, which might not be feasible for all users.
- User Experience: Offers an engaging experience but demands a high level of commitment and punctuality from users.
- Proof of Humanity
- Security: Combines video verification with vouching from existing members, creating a robust defense against fake identities.
- Accuracy: High, as it combines video verification with community vouching. However, there is a risk of human error or bias in the vouching process, which could affect the overall accuracy.
- Privacy: Personal videos may raise privacy concerns for some users.
- Scalability: Scaling is challenging due to the manual nature of video verification and vouching.
- Accessibility: The need for video submission and a vouch might pose barriers to entry for some users.
- User Experience: Provides a sense of community but requires a higher level of personal disclosure.
- WorldCoin
- Security: Uses biometric data (iris scans) to ensure the uniqueness of each user.
- Accuracy: Very high, given its reliance on biometric data (iris scans). Biometric verification is typically more accurate in ensuring unique identities, though there are concerns about false matches or exclusions, especially in large populations.
- Privacy: Biometric data usage raises significant privacy concerns, despite assurances of data security and the demand for additional details also raises concerns.
- Scalability: Scalability issues due to its hardware-based approach, are incapable of enrolling large populations quickly.
- Accessibility: Requires physical access to scanning hardware, which may not be available to all.
- User Experience: Fast and efficient but contingent on users' access to orbs (scanning devices).
- Humanode
- Security: Utilizes cryptobiometric technology to ensure 1 human = 1 node = 1 vote.
- Accuracy: Uses video-based uniqueness and liveness checks with 60+ AI modules that result in high accuracy. Like WorldCoin, the use of biometrics typically results in high accuracy, but risks of false positives or negatives exist.
- Privacy: High level of privacy protection due use of cryptobiometric and data processing in Confidential Virtual Machines.
- Scalability: Limited chain scalability to 10,000 validators
- Accessibility: Highly accessible as you only need a 3MP pixel camera on your phone to verify your existence and uniqueness.
- User Experience: Streamlined and quick for proofing users’ personhood with a quick facial scan. However, the process of becoming a validator node in the network is a bit cumbersome.
Each protocol offers a unique approach to establishing and safeguarding digital identity in the Web3 space. Their effectiveness and appropriateness can vary depending on their user base's specific needs and concerns, highlighting the diverse challenges and opportunities in the PoP domain.
Here's a more comprehensive comparison in the form of a Table.
Analysis of Most Popular PoP (PoP) Protocols
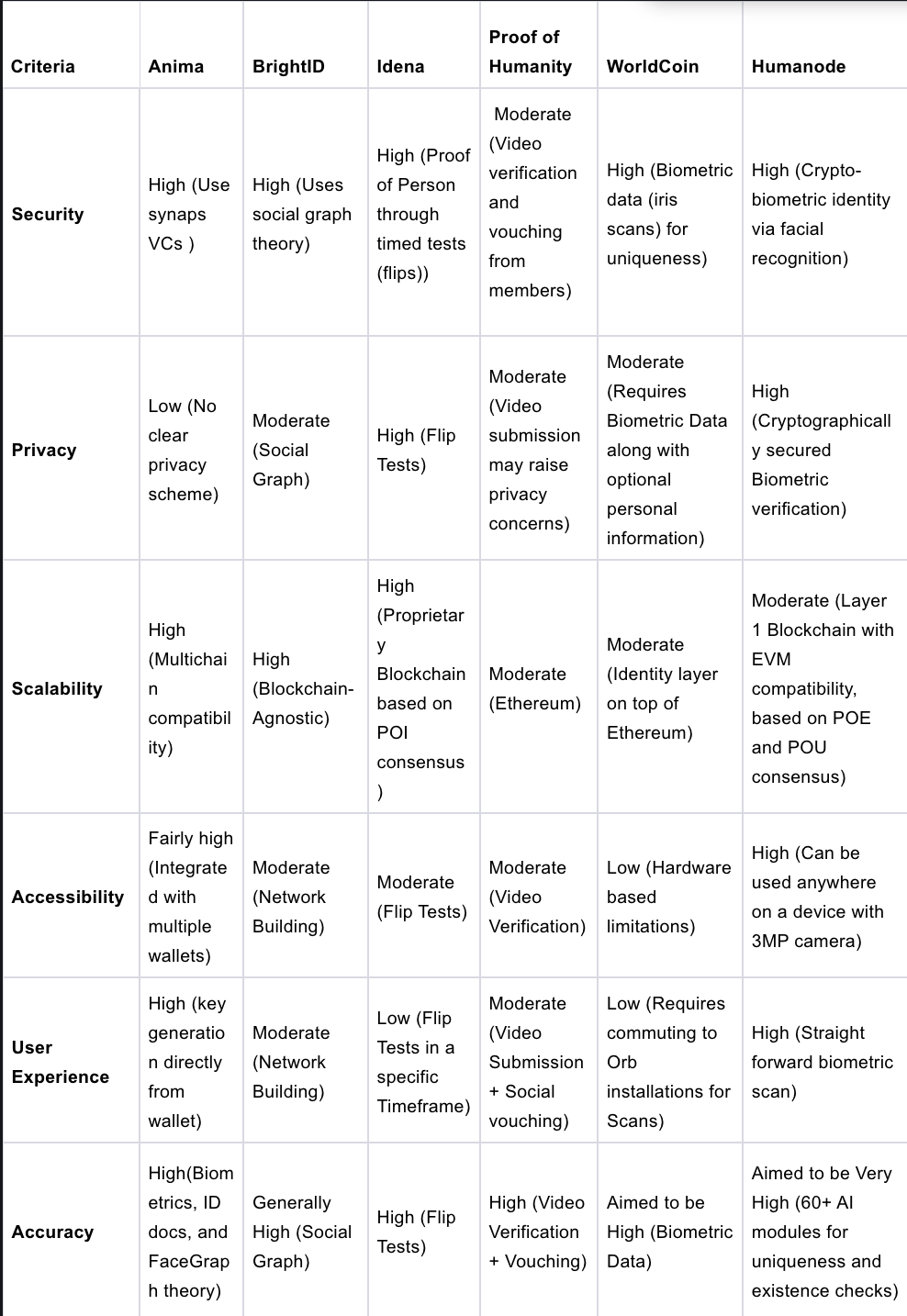
** Table 1 - Comparative Analysis
To provide a thorough comparison of the PoP protocols mentioned above, let's incorporate the additional points of comparison into our analysis:
Anima
- Underlying Blockchain: Anima is versatile across blockchains, including EVM chains and recent integrations with BNB and Cosmos, showcasing its adaptability.
- Decentralization Level: Upholds a high degree of decentralization, avoiding central points of control in its identity verification process.
- Community and Ecosystem: Building a robust and growing community, focused on diverse applications within the decentralized space.
- Real-World Adoption: In the early stages of real-world adoption, with potential use cases in DAO governance, regulatory compliance, and secure identity verification.
BrightID
- Underlying Blockchain: Blockchain-agnostic, compatible with multiple blockchains.
- Decentralization Level: Highly decentralized; no central authority controls the identity verification process.
- Community and Ecosystem: Robust and growing with diverse applications in the decentralized space.
- Real-world Adoption: Increasing adoption in decentralized applications for unique human verification.
Idena
- Underlying Blockchain: Uses its blockchain with a Proof of Identity (PoI) consensus mechanism tailored for the Idena protocol.
- Decentralization Level: Highly decentralized through collective intelligence and timed tests.
- Community and Ecosystem: Niche community with limited external ecosystem integrations.
- Real-world Adoption: Mainly within its network, with limited external applications.
Proof of Humanity
- Underlying Blockchain: Built on Ethereum.
- Decentralization Level: Decentralized, with community-based governance for verification.
- Community and Ecosystem: Strong support within the Ethereum community and integrated with its DeFi ecosystem.
- Real-world Adoption: Growing adoption in Ethereum-based applications for identity verification.
WorldCoin
- Underlying Blockchain: Blockchain-agnostic, aiming for universal applicability.
- Decentralization Level: Centralization concerns due to hardware dependency and data processing.
- Community and Ecosystem: Interest in large-scale identity solutions, but privacy and centralization concerns persist.
- Real-world Adoption: In early stages with pilot programs in various countries.
Humanode
- Underlying Blockchain: Layer 1 blockchain built on Proof of Existence and Proof of Uniqueness Consensus mechanism and compatibility with EVM blockchains
- Decentralization Level: Strives for a high level of decentralization through biometric-based node operation.
- Community and Ecosystem: Strong community and targeting applications in DeFi, Web2, and Web3 security, and governance that require reliable human identification.
- Real-world Adoption: Early stages, exploring applications in industries that demand secure and unique PoP including DeFi, Gaming, and P2P marketplaces.
Current Use Cases
Anima
- User Authentication in dApps: Potential to secure dApp identity verification for enhanced trust and security.
- Fair Reward Systems: Guarantees fair reward distribution by verifying participant uniqueness.
- Voting Systems and Polls: Can ensure each vote in decentralized systems is from a verified individual.
- Integration with Wallets: Smoothly integrates with major wallets for easy identity verification across platforms.
BrightID
- Gitcoin: Utilized for identity verification to prevent fraud in Gitcoin's quadratic funding mechanism.
- Idena Integration: Used in conjunction with Idena to enhance decentralized identity verification.
- 1Hive Communities: Deployed in 1Hive's decentralized autonomous organizations (DAOs) for unique human participation.
- Aragon: Integrated into Aragon for verifying unique identities in their governance platforms.
Idena
- QVote: Adopted in QVote for decentralized voting, ensuring one person, one vote.
- Subsocial: Used in Subsocial's decentralized social network for Sybil-resistant identity verification.
- Decentralized Forums: Employed in various forums to prevent spam and ensure genuine participation.
- Identity Layer in DApps: Integrated as an identity layer in multiple decentralized applications (DApps).
- 1person 1 node blockchain: Idena utilizes a Proof of Identity (PoI) consensus mechanism to run its blockchain where each user corresponds to a single node.
Proof of Humanity
- UBI Project: Central to the Universal Basic Income (UBI) project on Ethereum, verifying unique humans for UBI distribution.
- Snapshot: Used in Snapshot for Sybil-resistant governance voting in decentralized communities.
- Kleros: Integrated with Kleros for dispute resolution, ensuring participants are real humans.
- Decentralized Finance (DeFi): Utilized in various DeFi platforms to authenticate users.
WorldCoin
- Global UBI Projects: Pilot testing for universal basic income distribution.
- Decentralized Identity Verification: Trials in various decentralized platforms require unique human identification.
- Humanode: Exploring synergies with Humanode for enhanced biometric verification.
- Voting Systems: Piloted in voting systems requiring identity verification.
Humanode
- Financial Services: Applied in DeFi for Sybil-resistance and anti-fraud measures.
- Biometric-based LP staking: Applied successfully on the LP staking model to ensure Sybil resistance.
- Discord integration: BotBasher (a discord integration deployed by Humanode) is being used by discord communities for Sybil-resistance and 1 person1 spot airdrops, whitelisting, voting, and more.
- Private Biomapping: Pilot Testing by linking one EVM address to one person which has multiple use cases including but not limited to user authentication in DApps.
- Biometrically-Governed DAOs: Potential to be used in DAOs for biometrically validated voting and governance.
- 1 person 1 node blockchain: Humanode stands out by employing the Proof of Existence (PoE) and Proof of Uniquness (PoU) consensus in its blockchain operation, where each individual operates a single node.
While a majority of the use cases we discussed for each protocol mentioned above are more or less the same for every single one of these, Idena and Humanode stand out as the only protocols that use the PoP framework to run their blockchain network operations.
This framework offers a fair and equitable platform, fostering a truly decentralized environment. It ensures that network governance and decision-making processes are based on a wide and diverse human consensus, rather than being dominated by a few powerful entities, as is common in many other blockchain networks. Moreover, this enhances the network's security against coordinated attacks.
Future Outlook
The evolution of PoP protocols like Anima, BrightID, Idena, Proof of Humanity, WorldCoin, and Humanode is poised to redefine digital identity and trust in the digital realm. As these protocols mature, we can expect
- Wider Adoption in Web3: Increasing integration with decentralized platforms, and enhancing trust and security.
- Impact on Society and Governance: Potential to influence societal structures by providing equitable access to digital resources and fair governance.
- Advancements in Privacy and Security: Continued improvements to address privacy concerns, potentially reshaping how personal data is handled online.
- Global Identity Solutions: Possible emergence as standard solutions for global digital identity, influencing sectors from finance to social media.
- Innovative Applications: Emergence of new applications in areas like voting, social welfare, and content creation, leveraging unique identity verification.
The future implications of these PoP protocols extend far beyond the current Web3 applications, potentially transforming how identity is perceived and utilized across the internet and in society at large. Their development and adoption will be key in shaping a more secure, inclusive, and equitable digital world.